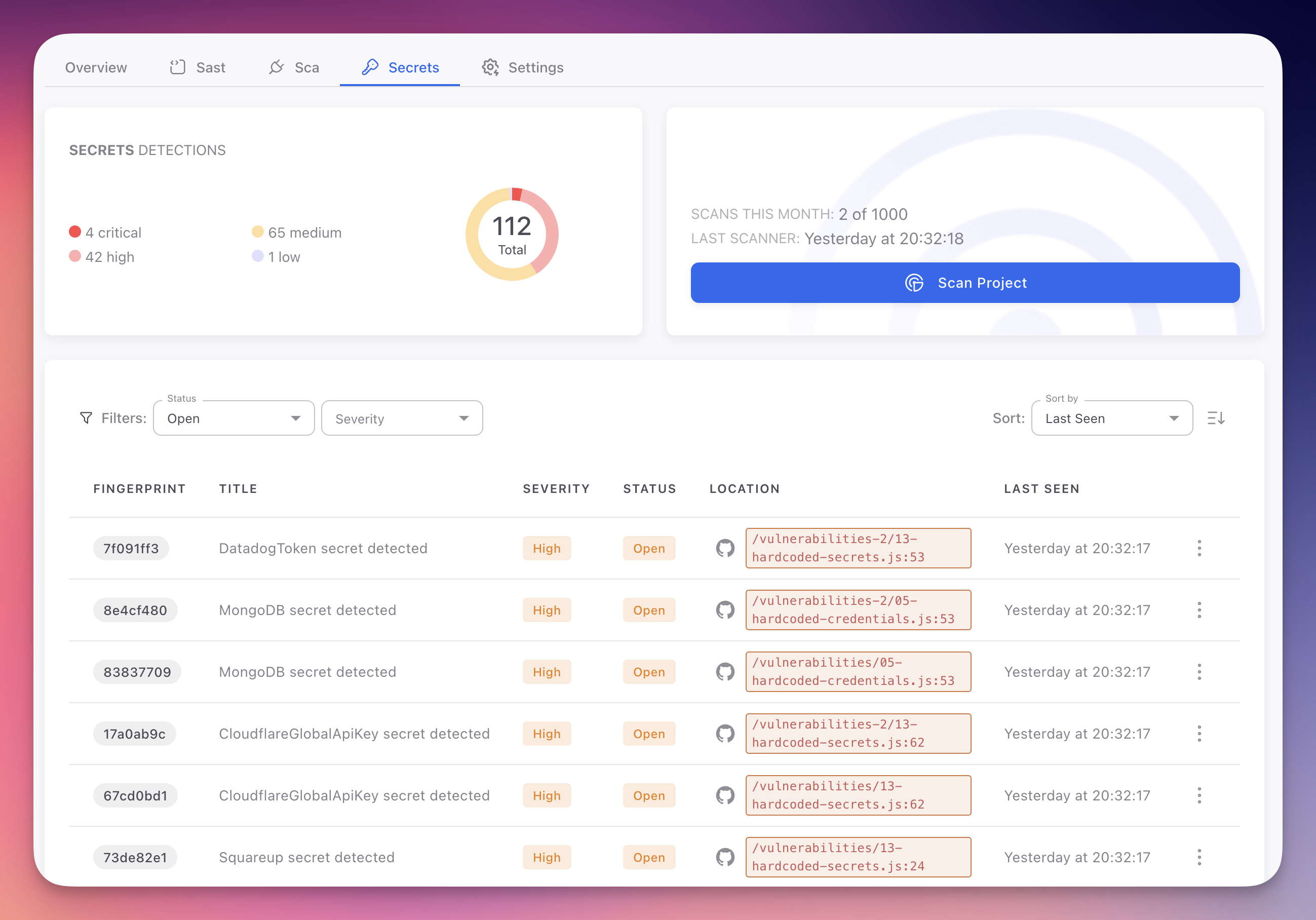
Secret Detection Overview
Secret Detection identifies hardcoded credentials, API keys, tokens, private keys, and other sensitive data in your source code. Leaked secrets are one of the most common causes of security breaches, and they persist in Git history even after being removed from the current codebase. Radar's secret detection engine combines pattern matching with entropy analysis to detect secrets with minimal false positives.
 Click to expand
Click to expand
Why Secret Detection Matters
| Factor | Impact |
|---|---|
| #1 credential leak vector | Developers routinely hardcode API keys, database passwords, and tokens during development and forget to remove them before committing. Even private repositories are not safe, as access controls change and repositories get forked or made public |
| Git history is permanent | Running git rm only removes the secret from the working tree. The credential remains in Git history and is accessible to anyone who clones the repository. Rewriting history is disruptive and often incomplete |
| Automated exploitation | Bots continuously scan public repositories for leaked credentials. A leaked AWS key can be exploited within minutes to spin up cryptocurrency mining infrastructure |
| Compliance impact | CWE-798 (Use of Hard-coded Credentials) is in the CWE Top 25. Hardcoded credentials violate SOC 2, PCI DSS, HIPAA, and GDPR requirements |
How Secret Detection Works
Radar uses a multi-layered approach to maximize accuracy and minimize false positives:
Pattern matching. Over 200 regex patterns for known credential formats across all major cloud providers, payment platforms, development tools, and communication services. Each pattern matches the specific format of a credential type (e.g., AWS Access Key IDs begin with
AKIAfollowed by 16 uppercase alphanumeric characters).Entropy analysis. Shannon entropy calculations detect high-entropy strings that resemble randomly generated secrets, even when they do not match any known pattern.
Contextual analysis. Examines variable names, file types, assignment context, and proximity to authentication-related function calls to reduce false positives. A high-entropy string assigned to
colorHexis treated differently from one assigned todatabasePassword.Multi-file correlation. Correlates findings across your entire codebase to identify where credentials are declared and consumed across different files.
AI-powered validation. Radar's AI engine analyzes each candidate to determine whether it is a real credential or a false positive. It recognizes patterns like hash digests in lock files, example values in documentation, encoded non-secret data, and test fixtures, reducing noise and surfacing only actionable findings.
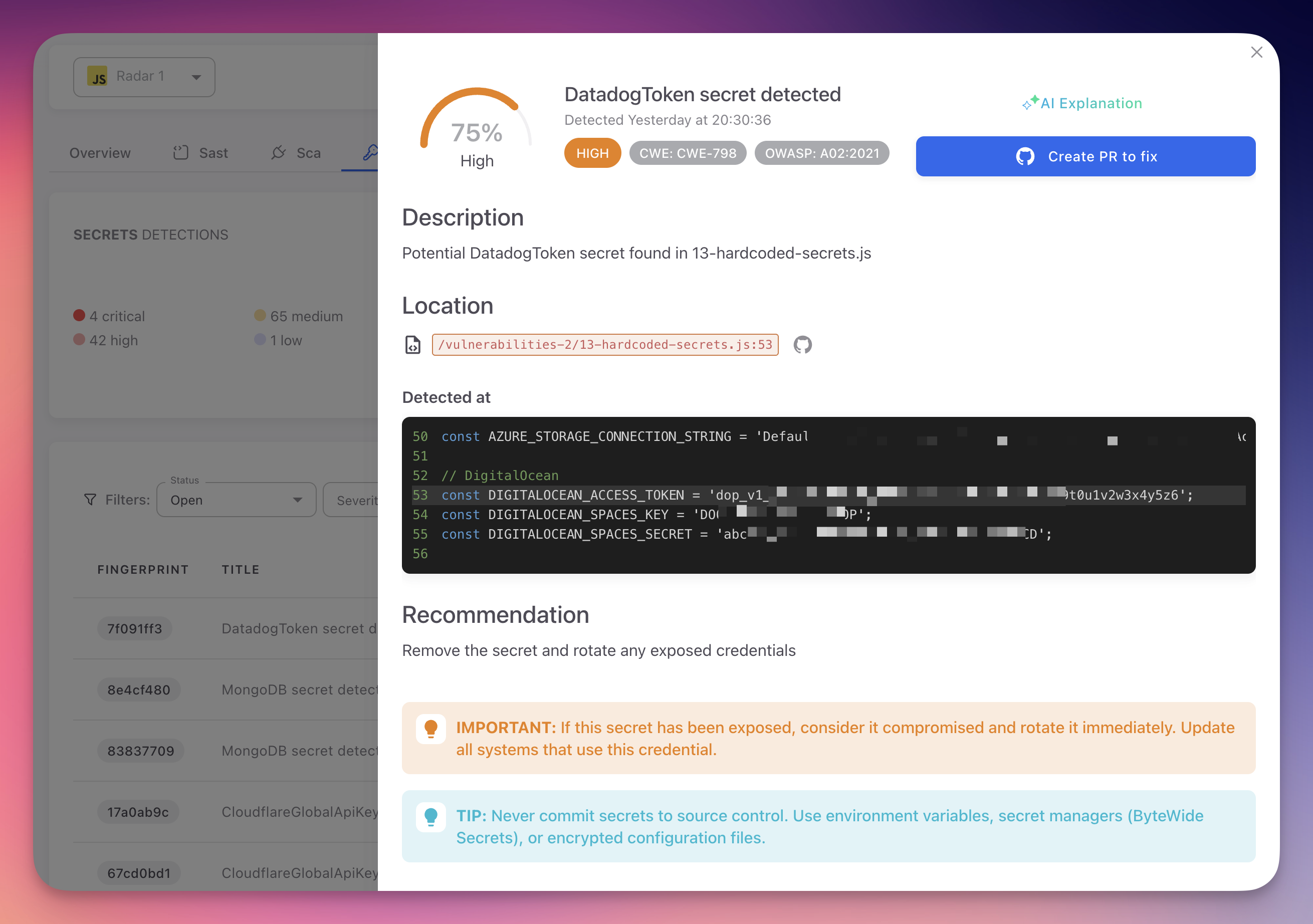
Finding Detail
 Click to expand
Click to expand
Each finding shows the secret type and confidence score, CWE and OWASP classification, file location with a direct GitHub link, a code snippet with the credential value partially masked, and a rotation recommendation. The AI Explanation tab provides a plain-language analysis of the risk and step-by-step remediation instructions specific to the credential type.
What Gets Detected
| Category | Examples |
|---|---|
| Cloud provider credentials | AWS access keys, Azure storage account keys, GCP service account keys, DigitalOcean tokens, Cloudflare API tokens |
| Payment service keys | Stripe secret keys, Square access tokens, PayPal client secrets |
| Database connection strings | MongoDB, PostgreSQL, MySQL, and Redis URIs with embedded passwords |
| API keys and tokens | GitHub, GitLab, Slack, SendGrid, Twilio, Mailgun, and other service tokens |
| Private keys and certificates | RSA, SSH, PGP private keys, and X.509 certificates with embedded private keys |
| Authentication secrets | JWT signing keys, OAuth client secrets, basic auth credentials, and bearer tokens |
| Generic high-entropy secrets | Randomly generated secrets detected through entropy analysis and contextual signals |
See Supported Secret Types for the complete list with detection patterns and remediation guidance.
Detection Confidence
| Detection Method | Confidence | Example |
|---|---|---|
| Known format patterns | Very high | AWS keys starting with AKIA, Stripe keys starting with sk_live_ |
| Entropy + strong context | High | High-entropy string in secrets.yaml assigned to api_token |
| Entropy + weak context | Medium | High-entropy string in a CSS file or generic variable name |
| AI context enhancement | Adjusted | Recognizes false positive patterns like hash digests in lock files, example values in documentation, and encoded non-secret data |
Automatic Vault Sync
When a secret is detected, Radar can automatically synchronize it to the ByteHide Secrets vault. The detected credential is stored securely in the vault with a unique key identifier, making it immediately available for secure retrieval through the Secrets SDK or API. This eliminates the gap between detection and secure storage.
AutoFix for Secrets
From any finding detail, click Create PR to fix to generate an automated pull request. Radar's AI agent offers two remediation strategies:
| Strategy | How It Works |
|---|---|
| Environment variable | Replaces the hardcoded value with an environment variable reference (e.g., process.env.DATADOG_TOKEN). Generates a .env.example with placeholder values. Works with dotenv or any environment configuration |
| ByteHide Secrets SDK | Replaces the hardcoded value with a call to the ByteHide Secrets SDK, referencing the secret by its vault key ID. The credential is managed, rotated, and retrieved securely at runtime with zero code changes needed for future rotations |
The second option provides full lifecycle management: the secret is detected, moved to the vault, and referenced by key. If the credential is rotated later, the application picks up the new value automatically without redeployment.
End-to-End in Seconds
Detection, vault sync, and code fix happen automatically. Radar detects the hardcoded credential, stores it securely in ByteHide Secrets, and generates a PR that replaces the hardcoded value with a secure SDK reference. Review, merge, and the risk is eliminated.
Secret Detection vs Secret Management
| Aspect | Secret Detection (Radar) | Secret Management (ByteHide Secrets) |
|---|---|---|
| Purpose | Find credentials that should not be in source code | Store and retrieve credentials securely at runtime |
| Type | Reactive control that catches mistakes after they happen | Preventive control that eliminates the need to put secrets in code |
| How they work together | Radar detects a hardcoded credential, syncs it to the vault, and generates a PR that replaces the value with a secure SDK reference | ByteHide Secrets stores the credential, manages rotation, and delivers it to the application at runtime |
Next Steps
Supported Secret Types
Complete list of credential types and patterns detected by Radar's secret detection engine.
View Secret Findings
Navigate, filter, and understand the secret findings table in your Radar project.
Triage and Remediation
The proper workflow for rotating, revoking, and remediating detected secrets.
ByteHide Secrets
Zero-knowledge secret manager designed to replace hardcoded credentials.