OWASP Top 10
The OWASP Top 10 is the most widely recognized standard for web application security risks. ByteHide Radar maps every SAST finding to the relevant OWASP categories: the Top 10 2025, Top 10 2021, and Top 10 for LLM Applications 2025, helping teams align their security efforts with industry standards and compliance requirements.
Supported OWASP Standards
Radar maps findings to the following OWASP standards:
| Standard | Edition | Focus |
|---|---|---|
| OWASP Top 10 | 2025 | Web application security risks (latest) |
| OWASP Top 10 | 2021 | Web application security risks (widely referenced in compliance) |
| OWASP Top 10 for LLM Applications | 2025 | AI and Large Language Model security risks |
Findings may map to categories in multiple standards simultaneously. For example, an SQL injection finding maps to both A05:2025 and A03:2021.
Compliance Alignment
Many compliance frameworks (PCI DSS, SOC 2, ISO 27001) reference the OWASP Top 10 directly or indirectly. Tracking your Radar findings by OWASP category provides ready-made evidence for audits and security assessments.
OWASP Top 10 2025 (Web)
Released in November 2025, based on analysis of over 175,000 CVE records. Two new categories were introduced and several were reorganized.
| ID | Category | Change from 2021 |
|---|---|---|
| A01:2025 | Broken Access Control | Same position. SSRF (A10:2021) merged in |
| A02:2025 | Security Misconfiguration | Moved up from A05:2021 |
| A03:2025 | Software Supply Chain Failures | New. Replaces A06:2021 with broader scope |
| A04:2025 | Cryptographic Failures | Moved down from A02:2021 |
| A05:2025 | Injection | Moved down from A03:2021 |
| A06:2025 | Insecure Design | Moved down from A04:2021 |
| A07:2025 | Authentication Failures | Renamed from A07:2021 |
| A08:2025 | Software or Data Integrity Failures | Same position |
| A09:2025 | Security Logging and Alerting Failures | Renamed from A09:2021 |
| A10:2025 | Mishandling of Exceptional Conditions | New. Improper error handling, failing open |
OWASP Top 10 for LLM Applications 2025
Dedicated to security risks in AI-powered applications. Radar's SAST engine detects code-level vulnerabilities that map to these LLM-specific risks.
| ID | Category | Description |
|---|---|---|
| LLM01:2025 | Prompt Injection | Untrusted input manipulates LLM behavior |
| LLM02:2025 | Sensitive Information Disclosure | Private data exposed through LLM interactions |
| LLM03:2025 | Supply Chain | Vulnerabilities in AI dependencies and models |
| LLM04:2025 | Data and Model Poisoning | Manipulated training data introduces backdoors |
| LLM05:2025 | Improper Output Handling | LLM output used unsafely in downstream systems |
| LLM06:2025 | Excessive Agency | AI agents with unrestricted permissions |
| LLM07:2025 | System Prompt Leakage | System prompts exposed to end users |
| LLM08:2025 | Vector and Embedding Weaknesses | RAG pipeline vulnerabilities |
| LLM09:2025 | Misinformation | LLM generates false but credible content |
| LLM10:2025 | Unbounded Consumption | Missing resource controls on LLM calls |
LLM + Traditional Risks
Many LLM vulnerabilities overlap with traditional OWASP categories. For example, LLM05 (Improper Output Handling) often results in injection vulnerabilities (A05:2025) when LLM output flows into SQL, HTML, or OS commands. Radar flags these with both OWASP and LLM category tags.
OWASP Top 10 2021 (Web)
The 2021 edition remains widely referenced in compliance programs. See the 2021 Reference for the full mapping between 2021 and 2025 categories.
| 2021 ID | Category | 2025 Mapping |
|---|---|---|
| A01:2021 | Broken Access Control | → A01:2025 |
| A02:2021 | Cryptographic Failures | → A04:2025 |
| A03:2021 | Injection | → A05:2025 |
| A04:2021 | Insecure Design | → A06:2025 |
| A05:2021 | Security Misconfiguration | → A02:2025 |
| A06:2021 | Vulnerable and Outdated Components | → A03:2025 (Supply Chain Failures) |
| A07:2021 | Identification and Authentication Failures | → A07:2025 |
| A08:2021 | Software and Data Integrity Failures | → A08:2025 |
| A09:2021 | Security Logging and Monitoring Failures | → A09:2025 |
| A10:2021 | Server-Side Request Forgery (SSRF) | → Merged into A01:2025 |
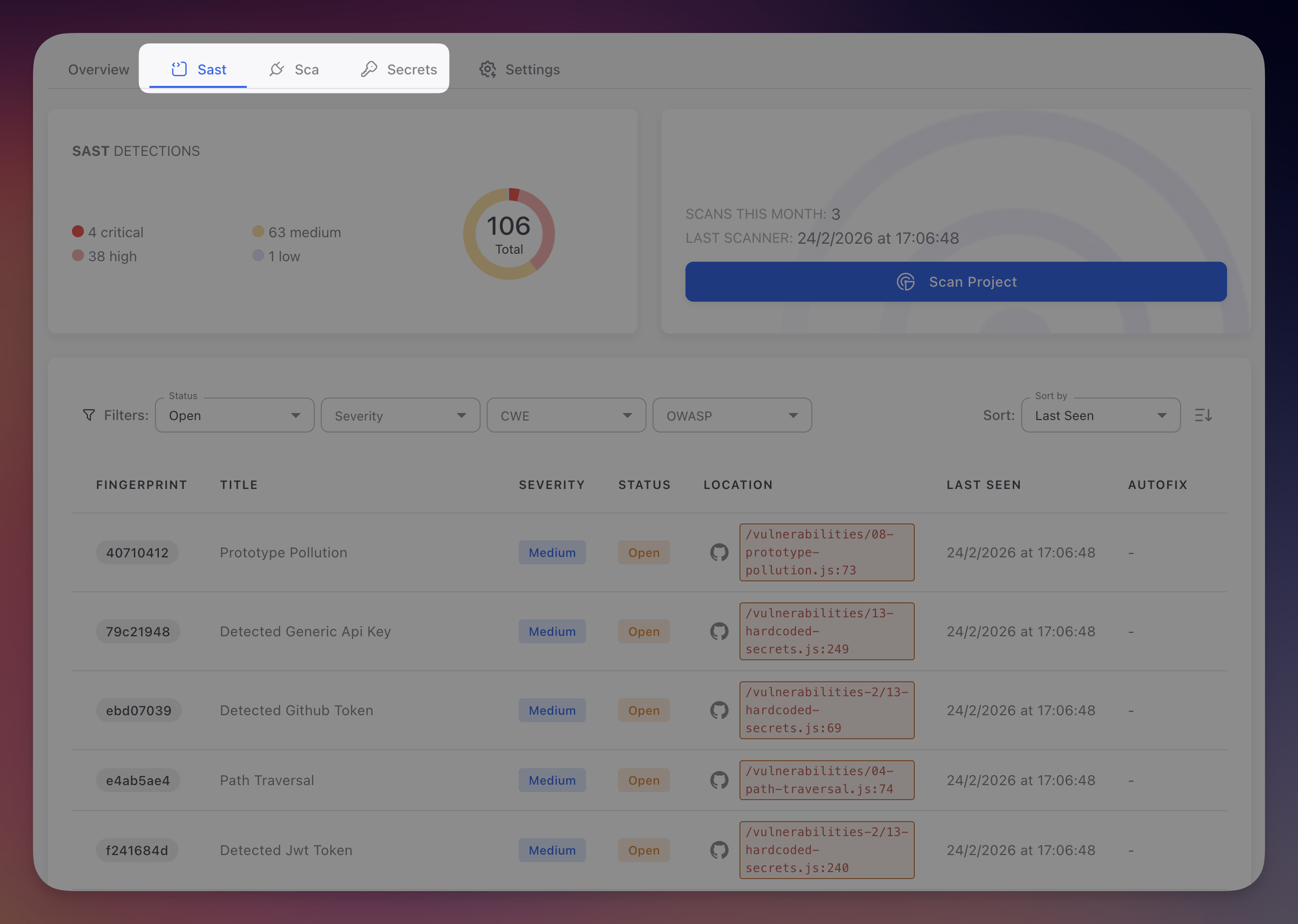
Using OWASP Filters in Radar
Filtering by Category
- Navigate to your Radar project's SAST tab
- Click the OWASP filter in the filter bar
- Select one or more categories (e.g., "A01:2025", "A05:2025", "LLM01:2025")
- The findings table updates to show only matching vulnerabilities
- Combine with the Severity filter to focus on Critical and High findings
 Click to expand
Click to expand
Compliance Reporting
OWASP category mapping enables streamlined compliance reporting:
- PCI DSS requires that all OWASP Top 10 vulnerabilities be addressed in payment-processing applications
- SOC 2 security criteria can be mapped to OWASP categories for evidence collection
- ISO 27001 Annex A controls align with several OWASP categories
Export filtered findings by OWASP category to generate evidence reports for auditors.
Tracking Progress
- Monitor the count of open findings per OWASP category across scan cycles
- Identify which categories have the most recurring findings, indicating systemic issues
- Set team goals to achieve zero Critical findings in specific OWASP categories
Beyond the Top 10
The OWASP Top 10 is a starting point, not a comprehensive checklist. Radar detects vulnerabilities beyond these categories, including ReDoS, prototype pollution, information leakage, and other weaknesses. Use the CWE filter for more granular classification.
Next Steps
CWE Reference
CWE identifiers used to classify SAST findings.
View SAST Findings
Navigate and filter the SAST findings table.
Triage and Remediation
Review, prioritize, and resolve findings.