SAST Overview
Static Application Security Testing (SAST) analyzes your source code without executing it to identify security vulnerabilities. Radar's SAST engine uses AI-powered analysis to understand code context and reduce false positives.
SAST operates directly on your source code, identifying vulnerabilities before code is deployed or merged. Radar integrates with your GitHub workflow to provide security feedback on every commit and pull request.
How SAST Works
Radar parses your source code and applies security rules across multiple analysis dimensions:
Data Flow Analysis
Traces how user-controlled input moves through your application. Follows variables from their source (HTTP parameters, form inputs, API payloads) through transformations to sensitive operations (database queries, file access, command execution). When untrusted data reaches a sensitive operation without sanitization, Radar flags an injection vulnerability.
Control Flow Analysis
Examines execution paths to identify logic errors and access control issues. Maps all branches, loops, and exception handlers to determine whether security-critical operations are consistently protected. Detects missing authorization checks, race conditions, and silenced security exceptions.
Semantic Analysis
Understands what your code does beyond syntax. Recognizes security-relevant patterns even when expressed differently. For example, constructing an SQL query through string formatting is functionally identical to concatenation, and both are vulnerable to injection with user input.
AI Context Analysis
Evaluates each potential finding against the surrounding code context and patterns learned from real-world codebases. Distinguishes between genuine vulnerabilities and safe patterns that match a rule signature, reducing false positive rates.
What SAST Detects
Every finding is mapped to CWE identifiers and OWASP Top 10 categories.
| Category | Examples |
|---|---|
| Injection Flaws | SQL injection, NoSQL injection, LDAP injection, command injection, code injection, XPath injection |
| Cross-Site Scripting (XSS) | Reflected XSS, stored XSS, DOM-based XSS |
| Broken Access Control | Insecure direct object references (IDOR), missing authorization checks, privilege escalation |
| Security Misconfiguration | Hardcoded credentials, insecure defaults, verbose error messages, debug mode enabled |
| Insecure Deserialization | Unsafe object deserialization (BinaryFormatter, pickle, ObjectInputStream), prototype pollution |
| SSRF | Unrestricted URL access, internal service exposure (cloud metadata endpoints) |
| Path Traversal | Directory traversal (../ sequences), file inclusion with user-controlled paths |
| Cryptographic Failures | Weak algorithms (MD5, SHA1, DES), insecure random generation, missing encryption |
| XXE | XML parser misconfiguration, entity expansion attacks |
| CSRF | Missing anti-forgery tokens on state-changing endpoints |
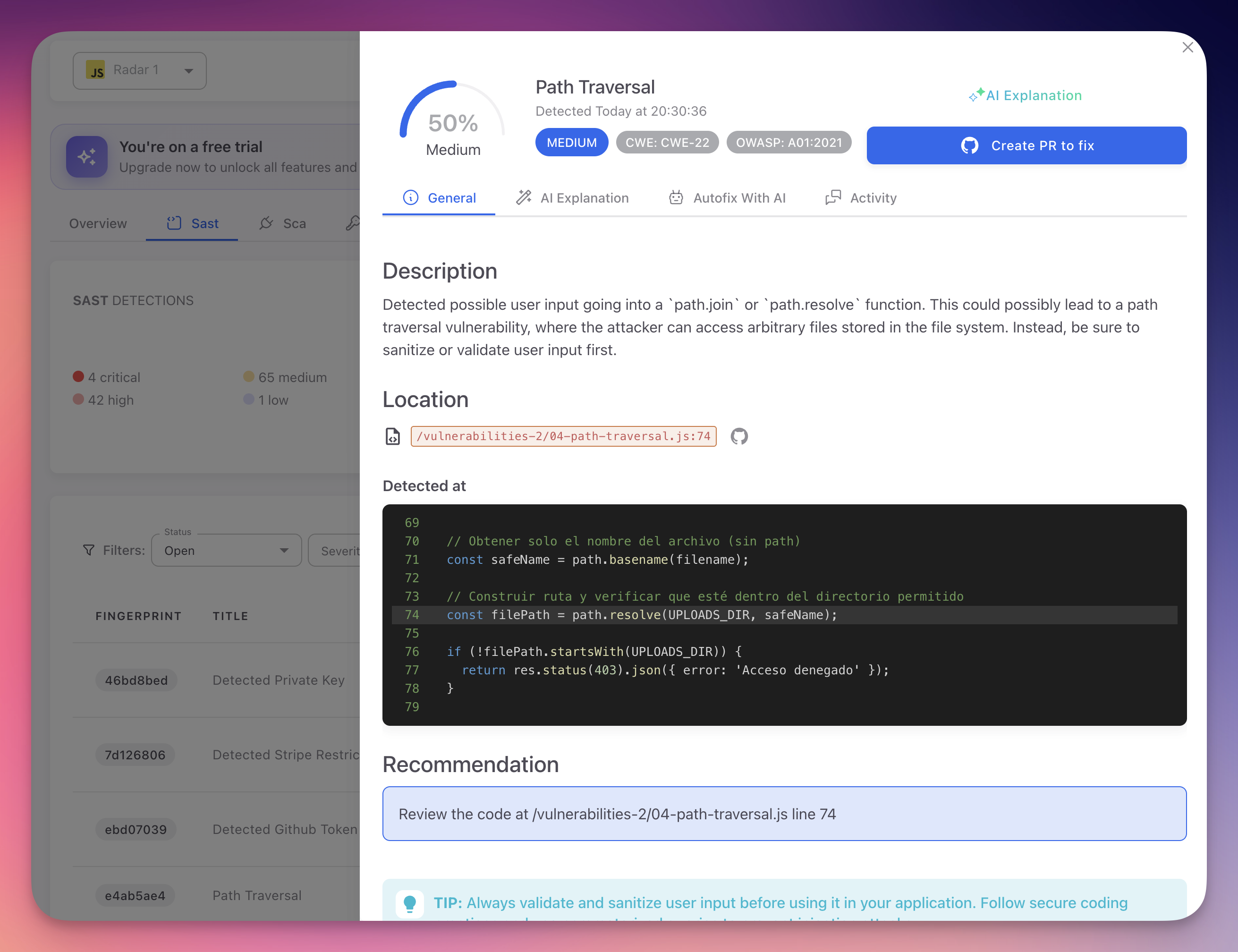
Finding Detail
When you click on a finding, Radar shows the full analysis:
 Click to expand
Click to expand
Each finding includes:
| Section | Description |
|---|---|
| Severity and Confidence | Confidence percentage (0-100%) and severity level (Critical, High, Medium, Low) |
| CWE and OWASP | Mapped to CWE identifier and OWASP Top 10 category |
| Description | What the vulnerability is and why it matters |
| Location | File path and line number with a direct link to the code on GitHub |
| Code Snippet | The vulnerable code with the affected line highlighted |
| Recommendation | Specific guidance on how to fix the issue |
| Create PR to fix | Generate an AI-powered fix and open a pull request. See AutoFix |
The finding detail also has tabs for:
- AI Explanation - Detailed AI-generated explanation of the vulnerability and its impact
- Autofix With AI - Preview and apply the AI-generated code fix
- Activity - History of status changes and comments
Severity Levels
| Level | Description | Example |
|---|---|---|
| Critical | Exploitable vulnerabilities leading to system compromise or data breach | Unauthenticated SQL injection on a public endpoint |
| High | Serious vulnerabilities with significant impact if exploited | Stored XSS targeting admin users, authentication bypass |
| Medium | Exploitable under specific conditions or requiring additional factors | Reflected XSS requiring social engineering, CSRF on non-critical functions |
| Low | Best practice violations with limited direct impact | Missing security headers, verbose error messages in non-production |
Each finding also includes a confidence score (0-100%) based on exploitability, impact, and the AI engine's certainty that the finding is genuine.
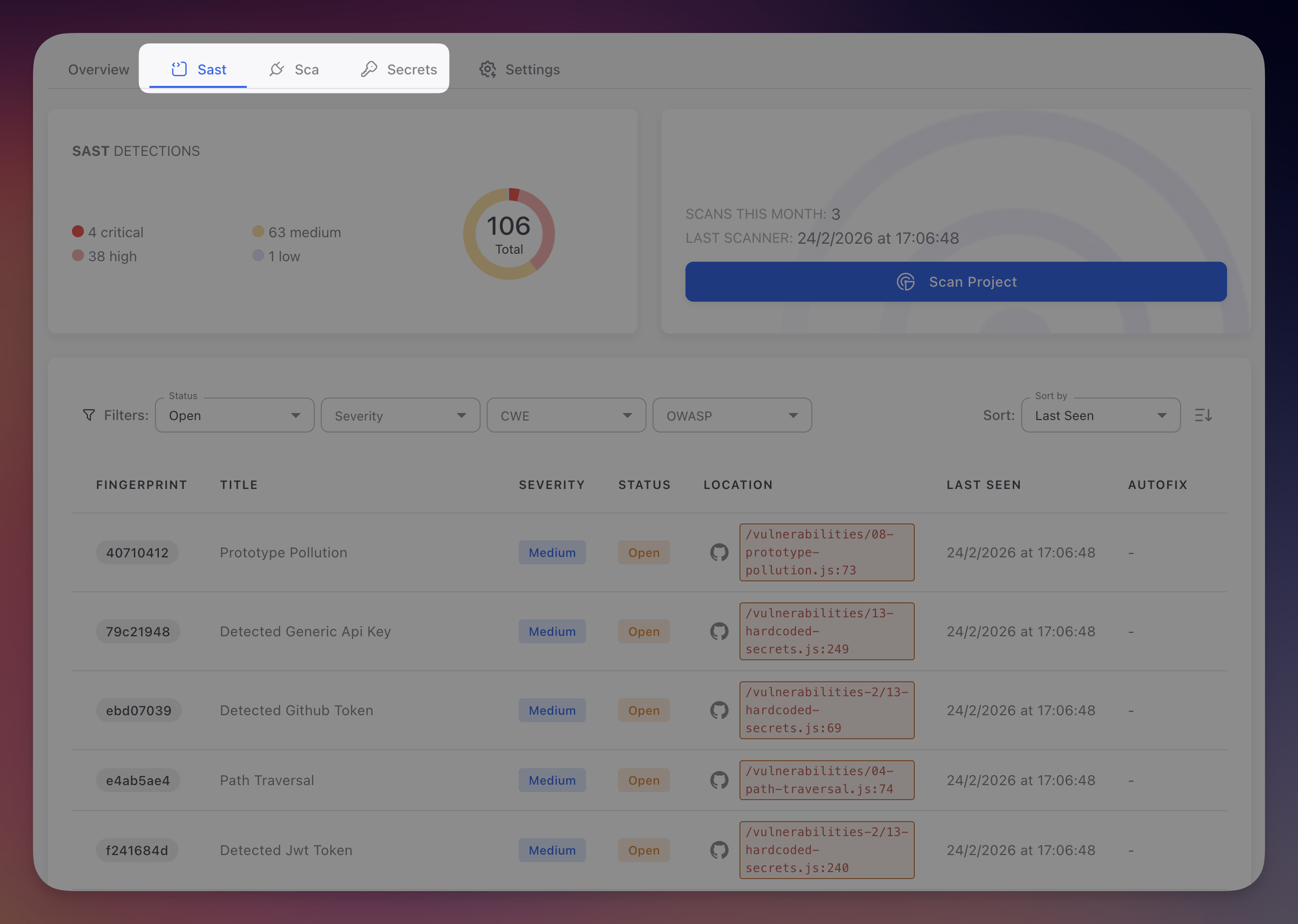
SAST Findings Table
The SAST tab shows all findings with filters for Status, Severity, CWE, and OWASP:
 Click to expand
Click to expand
See View SAST Findings for the full guide on navigating, filtering, and triaging findings.
Next Steps
Supported Languages
Languages and frameworks analyzed by Radar's SAST engine.
View SAST Findings
Navigate, filter, and understand the SAST findings table.
CWE Reference
CWE identifiers mapped to Radar's SAST findings.
OWASP Top 10
How Radar maps findings to OWASP Top 10 categories.