SCA Overview
Software Composition Analysis (SCA) identifies vulnerabilities in third-party dependencies and open-source libraries used in your application. Radar's SCA engine scans your dependency manifests and lock files to detect packages with known security vulnerabilities (CVEs), providing severity scores, remediation guidance, and upgrade recommendations.
While SAST focuses on vulnerabilities in the code you write, SCA focuses on vulnerabilities in the code you use. Together, they provide comprehensive security coverage across your entire application surface.
 Click to expand
Click to expand
Why SCA Matters
| Factor | Impact |
|---|---|
| Open-source is pervasive | 80-90% of modern applications is open-source code. The majority of your attack surface resides in third-party packages |
| Single points of failure | A single vulnerable dependency can expose your entire application. Log4Shell (CVE-2021-44228) affected millions of apps regardless of first-party code quality |
| Continuous threat landscape | New CVEs are published daily. A dependency that was secure three months ago may have a critical vulnerability disclosed today |
| Hidden transitive risk | Your 20 direct dependencies can pull in hundreds of transitive packages. Vulnerabilities anywhere in this tree affect your application |
Supply Chain Security
SCA is a foundational element of software supply chain security. By continuously monitoring your dependency tree, you reduce the risk of shipping exploitable code from third-party packages.
How SCA Works
Identify dependency manifests. Radar automatically detects manifest files (
package.json,requirements.txt,pom.xml,.csproj,go.mod,composer.json,Gemfile) in your repository. No configuration needed.Parse the dependency tree. Parses both direct and transitive dependencies from lock files (
package-lock.json,yarn.lock,Pipfile.lock, etc.). Lock files provide exact resolved versions for precise matching. When lock files are unavailable, Radar resolves from manifest declarations.Cross-reference vulnerability databases. Each package and version is checked against the NVD, GitHub Advisory Database, and ByteHide's own vulnerability intelligence. Radar aggregates multiple sources for comprehensive, up-to-date coverage.
Generate findings and recommendations. For each vulnerable dependency, Radar calculates severity from CVSS scores and generates remediation recommendations. When a patched version exists, Radar identifies the minimum safe version and can generate an AutoFix pull request to upgrade.
What SCA Detects
| Category | Description |
|---|---|
| Direct dependency CVEs | Vulnerabilities in packages you explicitly declare in your manifest files. Straightforward to remediate since you control the version directly |
| Transitive dependency CVEs | Vulnerabilities in packages pulled in by your direct dependencies. Radar traces the dependency path so you know which direct dependency introduces the risk |
| Outdated packages with patches | Dependencies where the installed version has a known vulnerability and a newer version with a security fix is available |
| Malicious packages | Packages flagged as containing malicious code, including typosquatting attacks, compromised maintainer accounts, and dependency confusion exploits |
Severity Levels
| Level | CVSS Score | Description | Example |
|---|---|---|---|
| Critical | 9.0 - 10.0 | Immediately exploitable, often with public exploits. Remote code execution, full data access, or complete system compromise | Log4Shell, Spring4Shell |
| High | 7.0 - 8.9 | Significant risk with moderate exploitation effort. May require authentication or specific configurations | Privilege escalation, data theft |
| Medium | 4.0 - 6.9 | Exploitable under specific conditions or with social engineering | DoS under specific configs, CSRF |
| Low | 0.1 - 3.9 | Limited impact and difficult to exploit | Non-sensitive information disclosure |
Vulnerability Databases
Radar aggregates data from multiple sources so that a vulnerability reported in one database but not yet in another is still detected.
| Database | Maintained By | What It Provides |
|---|---|---|
| NVD (National Vulnerability Database) | NIST (U.S. government) | CVSS scores, CWE mappings, CPE entries, structured version ranges |
| GitHub Advisory Database | GitHub (community-curated) | Ecosystem-aware version ranges (npm, NuGet, Maven, PyPI, RubyGems, Go), package-level granularity |
| ByteHide Vulnerability Intelligence | ByteHide | Proprietary database with additional coverage, zero-day advisories, and malicious package signatures not yet cataloged in public databases |
Monitor Correlation
When ByteHide Monitor is active in your application, runtime detections feed back into Radar. If Monitor detects a malicious library, suspicious dependency behavior, or a vulnerability being exploited at runtime, the finding is automatically synchronized to your Radar SCA tab. This gives you a unified view that combines static dependency analysis with real-world runtime signals, so you can prioritize the vulnerabilities that are actually being triggered in production.
Next Steps
Supported Ecosystems
Package ecosystems and manifest formats analyzed by SCA.
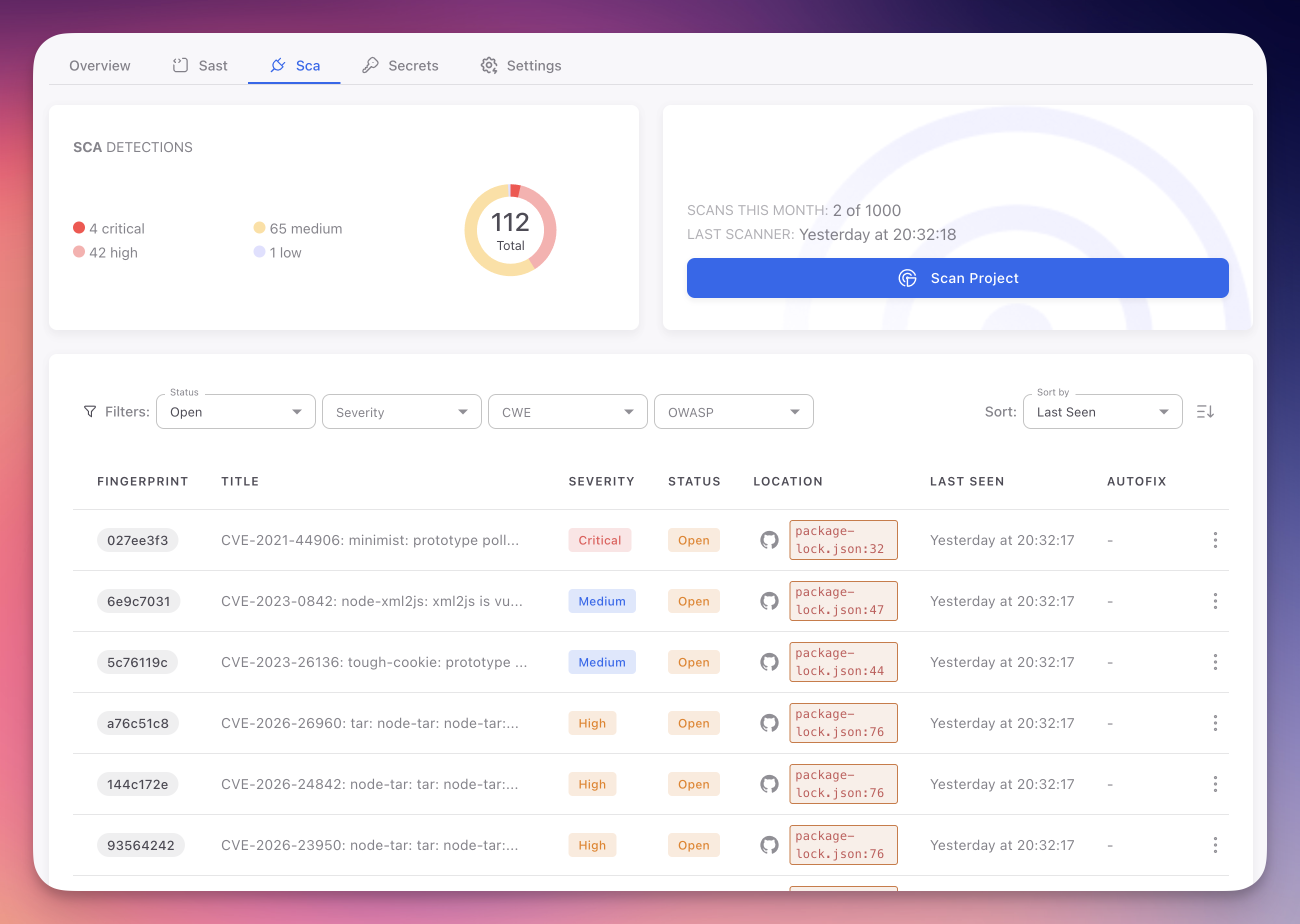
View SCA Findings
Navigate, filter, and understand the SCA findings table.
CVE Reference
CVE identifiers, CVSS scoring, and vulnerability databases.
Detect Vulnerable Dependencies
How Radar maps your full dependency tree.